With thanks to Darin Filler who first posted this on FaceBook
I found some interesting information in my FaceBook “memories” yesterday. So interesting, in fact, that I have to share it …
“Dr Ross Adey
Mind control
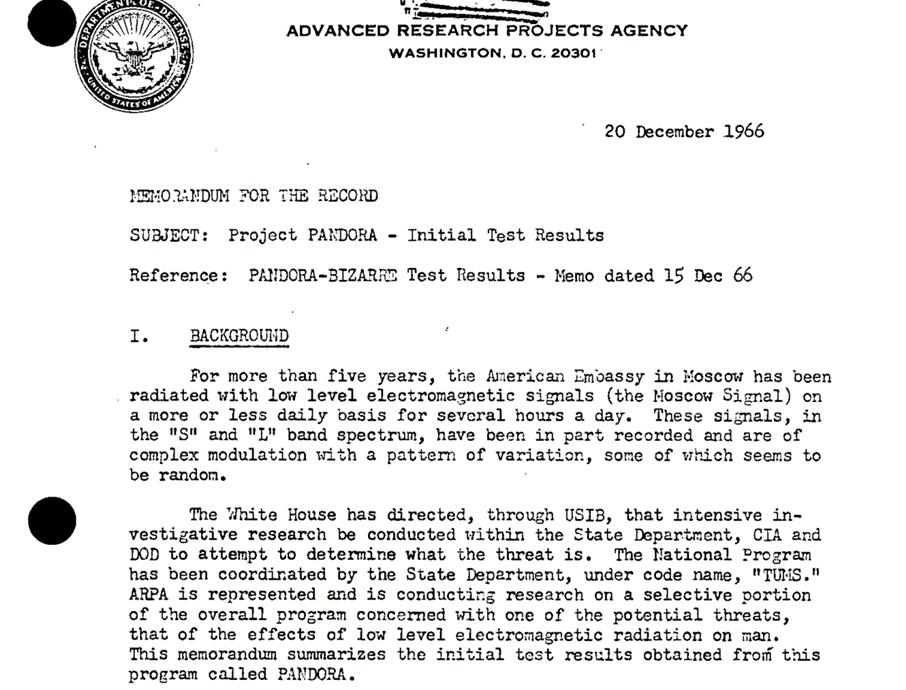
Dr Ross Adey, formerly of the Brain Research Center at the University of Southern California, and now at the Loma Linda University Medical School, California, worked on the CIA’s infamous Pandora project. His research involved inducing of specific behaviour modifications by electromagnetic means, as well as inducing calcium efflux events to interfere with brain function-the so-called “confusion weaponry”. (More recently, Dr Adey has been warning against the biological hazards of EM emissions from mobile phones.)
Dr Adey’s research at the Brain Research Center has shown the existence of a biological reaction to EM radiation. This reaction was found to be dependent on the frequency, amplitude and dose of the microwave radiation used.
In the 1980s Dr Adey performed some crucial experiments using microwave carrier-waves modulated with ELF waves to modify brain tissue responses. He carried out experiments with cat brain tissue, showing that the binding of calcium ions to neuronal sites was affected by weak EM fields. These fields were of a frequency and amplitude similar to fields produced in mammalian bodies and detected on electroencephalographs (EEGs).
Dr Adey demonstrated how a 147-megahertz (MHz) field, which at tissue level had an intensity of 0.8 milliwatts per square centimetre, caused an efflux or release of calcium ions from the irradiated brain tissue. This response only occurred when the ELF modulation of the microwave carrier-wave had an amplitude modulated at 6-20 hertz (Hz). The maximum stimulation of the neurones took place at 16 Hz, but to either side of this frequency-range parameter there was no effect.8 [1996 Nexus] REMOTE VIEWING: THE STORY OF THE REAL X FILES By Turan Rifat
Secondly, the police have been granted the exclusive use of the 450 MHz microwave frequency range. This is exactly the frequency used by Dr Ross Adey, the CIA mind control expert, in his experiments on behavioural modification. It seems the police have the exclusive use of this mind control frequency and a vast array of antennae to broadcast this frequency all over the country. Very useful for mass mind control in times of emergency. Adey found that by using 0.75mW/cm2 intensity of pulse modulated microwave at a frequency of 450 MHz, it was discovered that an ELF modulation could be used to control all aspects of human behaviour. The Sussex police headquarters is connected to CCTV, closed circuit television cameras throughout the town. Some of these cameras have microwave telemetry devices that could easily be used to broadcast this frequency. The large antennae that bracket the town could also be used. MICROWAVE MIND CONTROL by Tim Rifat
By use of my microwave detector, I have found that mobile phones of the newer type, give off a pulse modulated microwave signal of around 0.75mW/cm2 at the earpiece. This may be coincidence, but it is exactly the intensity required form behavioural control as found by Dr Ross Adey, the pioneer of microwave mind control. So in theory, an ELF signal could be added to the microwave network to feed a precise behavioural pattern into every mobile phone user in the UK. If their were widespread riots, the ability to broadcast behavioural stimuli to mollify all the mobile phone users in the country would prove useful. Since mobile phone users are generally middle class, it means authority has a useful method of controlling the behaviour of the key voters. Microwave carrier beams are perfect for transmitting the excitation potential of docility to the phone user to keep them servile in times of trouble. When no ELF signal is broadcast the phone acts in a completely different manner on behaviour in humans. In this case the microwave phones causes the neurones to release calcium ions which makes the user tired irritable and when stresses likely to emotional outbursts such as road rage. MICROWAVE MIND CONTROL by Tim Rifat
The TETRA system pulses at 17.6 Hz broadcast at 400 MHz which is essentially the Pandora Project funded by the CIA in the late ’60s and early ’70s. Dr Ross Adey, the chief researcher on the Pandora Project has released a video to leading UK researchers which proves that not only does the TETRA system cause ELF zombification by massive release of calcium ions in the cerebral cortex and the nervous system, but the activated calcium ions also cause massive hormonal disturbances which lead to frenzied imbalances, emotional and physical states……
Use of the TETRA system by the police will lead to psychotronicaly controlled officers who may be totally controlled in any situation and are very useful for states of economic or social chaos where extreme and violent behaviour is needed without any conscious or moral compunction – so-called police robots. [2001] The TETRA System: Mass UK Mind Control Technology and the Zombification Of Britain’s Police is Now A Reality by Tim Rifat
One of the first voices in the West to raise concern was Professor Ross Adey. Although interested in radio and the development of radar from an early age, he qualified in medicine in Australia during the war and then came to Oxford to study brain physiology. He was appointed as a professor at University of California in 1954 and in 1961 joined their newly formed Brain Research Institute. In 1965 he was appointed as Director of the new Space Biology Laboratory. The projects his teams worked on were related to brain activity of service personnel, including the effects of pulsed ELF and microwave radiation, and were funded by NASA, ARPA, NSF, USAF and USN. Since then he has remained at the forefront of research into these matters. He commented recently “I would be very concerned about a four-watt Tetra hand-held radio against my head day after day”.
So what is the cause of this concern? Back in the mid-1960s Adey and colleagues revolutionised our understanding of the way brains cell operate. During the next 20 years many papers were published showing that ELF electromagnetic fields affected the way calcium ions move in brain tissue and the way this affects the inner working of the cells. Living cells are enclosed by a strong protective membrane (skin) and communicate with the outside world through electrically charged protein strands that stick out from their surface. These carry signals into the cell interior where they regulate growth, development and cell division. By 1976 low level electromagnetic field effects had been shown to occur across the ELF range, peaking between about 12 and 20 Hz. The effects were seen most clearly with the ELF signals amplitude modulated on to microwaves, such as those that TETRA handsets use. The microwaves penetrate brain tissue and effectively ‘carry’ the ELF pulsing deep into the brain. There is also considerable evidence that low levels of pulsed microwaves can cause the blood-brain barrier to allow toxins to reach the brain. [March 2001] Alasdair Philips, Director of Powerwatch, examines the potential hazards of TETRA… The negative aspects of TETRA ..”
https://constantinereport.com/cia-mind-control-history-uclas-dr-w-ross-adey-brain-telemetry/